
Hackers use not only Google but also Microsoft Sharepoint for advanced phishing campaigns.
Check Point Research (CPR), the threat intelligence division of Check Point® Software Technologies Ltd. presents the third case of misusing a legitimate tool to disguise phishing campaigns. In addition to Google Collection and Google Ad, Microsoft SharePoint is now being added. The program is mainly used to send phishing e-mails to give them a deceptively real look.
How hackers use Microsoft Sharepoint
The security researchers describe how hackers misuse the program to send phishing emails. An example:
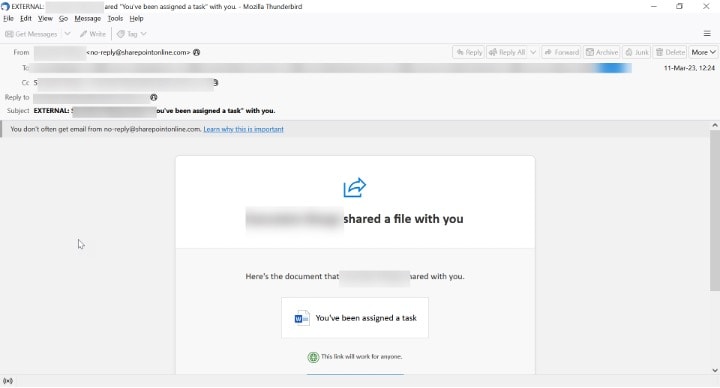
Someone receives a message from Microsoft SharePoint that a file has been shared (Image: CheckPoint)
The link leads to a legitimate SharePoint page:
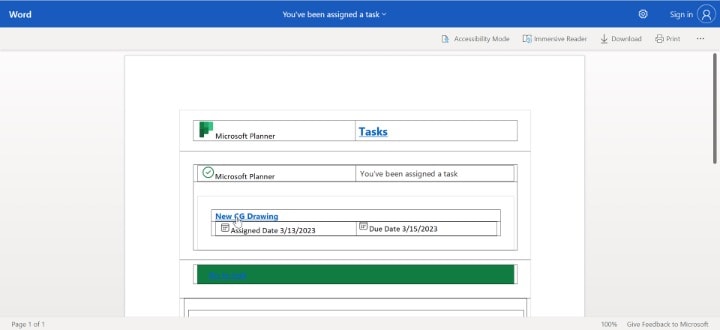
The "New CG drawing" stored there does not lead to another Microsoft address, but to a phishing page (which has since been removed). However, all other links are legitimate. (Image: CheckPoint)
Security researchers advise extreme caution
Link protection, which simulates the web pages behind the links in order to check them, helps above all against these attacks. Even after the user clicks on the deceptive SharePoint link, he can still analyze it. In addition, there must be an analysis program for zero-day phishing signs from web pages and OCR for detecting fake symbols and logos.
However, the security researchers would like to point out that neither Google nor any of its services would now be dangerous or illegitimate. This is indicated by the small addition under the Google form: "This content is neither created nor endorsed by Google." The hackers are simply abusing Google Collection. Check Point notified Google of this vulnerability on July 5, 2023.
The security researchers advise companies and private users to exercise great caution. They also recommend implementing AI-powered IT security solutions that can look out for various indicators, introducing an email security solution that checks documents and files, and a URL security solution that checks and emulates websites.
More at CheckPoint.com
About check point Check Point Software Technologies GmbH (www.checkpoint.com/de) is a leading provider of cybersecurity solutions for public administrations and companies worldwide. The solutions protect customers from cyberattacks with an industry leading detection rate for malware, ransomware and other types of attacks. Check Point offers a multi-level security architecture that protects company information in cloud environments, networks and on mobile devices, as well as the most comprehensive and intuitive “one point of control” security management system. Check Point protects over 100.000 businesses of all sizes.
Matching articles on the topic
