
New phishing campaign from the Business E-Mail Compromise area discovered: Hackers disguise their activities behind the Google Collection tool.
Check Point Research (CPR), the threat intelligence division of Check Point® Software Technologies Ltd. has discovered that hackers are abusing the Google Collection. They benefit from the tool's ability to save and share links, images and videos on the one hand and the Google brand to make their phishing emails appear legitimate on the other.
The security researchers describe how hackers misuse Google's pages to send links to fake cryptocurrency sites.
This is what the Google Collection Phishing campaign looks like:
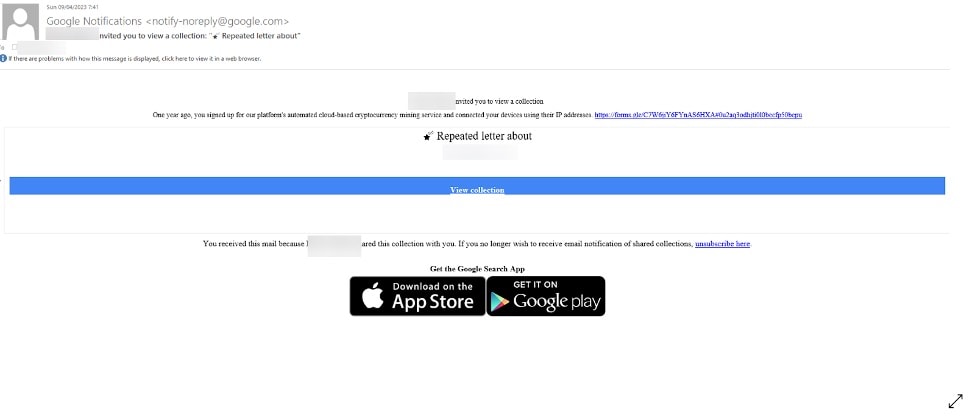
(Image: CheckPoint)
The email comes to the user in the usual style, even with a Google notification, since the hacker simply shared his collection with the user. The email was sent from a no-reply(at)google.com address, which is legitimate. The link itself is not infected either, as it leads to a legitimate Google page. One of the well-known Google Collection cards will appear there:
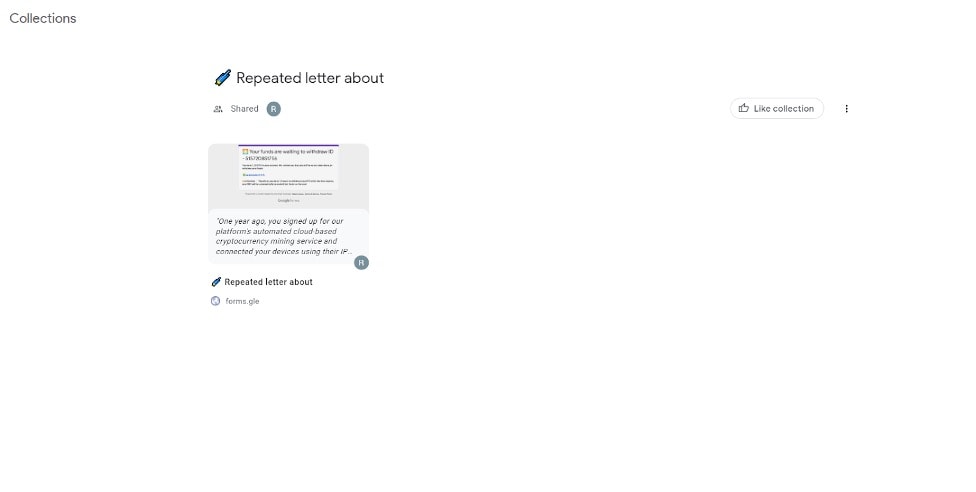
(Image: CheckPoint)
Links to images, videos or websites can be stored on such cards. This hacker map leads to the following Google form:
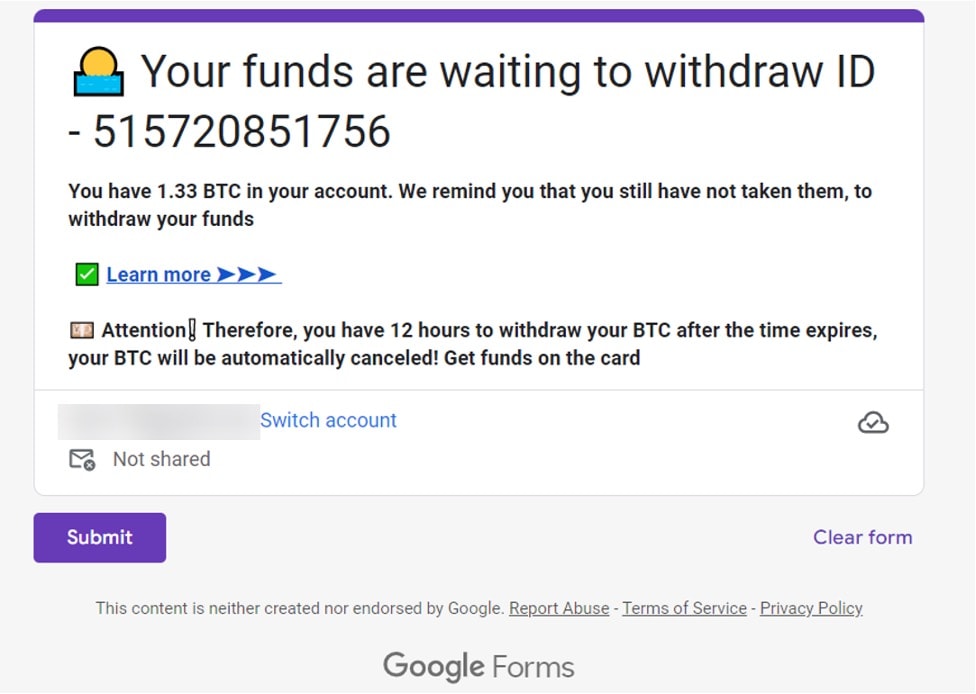
(Image: CheckPoint)
Because it's a Google Forms form, which is legitimate, it doesn't suffer from the usual phishing anomalies, such as misspellings or fake looks. However, that last link then leads to the genuinely fake cryptocurrency website designed to steal users' funds.
However, the security researchers point out that neither Google nor any of its services are now dangerous or illegitimate. This is indicated by the small addition under the Google form: "This content is neither created nor endorsed by Google." The hackers are simply abusing Google Collection. Check Point notified Google of this vulnerability on July 5, 2023.
More at CheckPoint.com
About check point Check Point Software Technologies GmbH (www.checkpoint.com/de) is a leading provider of cybersecurity solutions for public administrations and companies worldwide. The solutions protect customers from cyberattacks with an industry leading detection rate for malware, ransomware and other types of attacks. Check Point offers a multi-level security architecture that protects company information in cloud environments, networks and on mobile devices, as well as the most comprehensive and intuitive “one point of control” security management system. Check Point protects over 100.000 businesses of all sizes.
Matching articles on the topic
