
A few days ago, Kaspersky discovered sophisticated malware on company iPhones. The campaign, dubbed Operation Triangulation, is apparently even more dangerous than, say, Pegasus, with which even heads of state like Macron were overheard. Kaspersky analyzed the malware and released the free triangle_check tool for macOS, Windows and Linux, which looks for the malware infection.
It sounds more like something out of a spy film: an APT group develops malware tailored to a specific iPhone vulnerability and uses it to infect the iPhones of a major security provider. The attacker must have unlimited self-confidence. But the attacker did not expect how secure it is internally at Kaspersky:
Since Kaspersky meticulously monitors and always analyzes all communications on its own network, it has been noticed that various iPhones are doing strange things. The detected APT campaign targets iOS devices. Further analysis revealed that the threat actor had infected iOS devices belonging to dozens of company employees.
Kaspersky internal iPhones infected
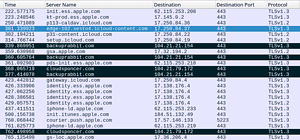
🔎 According to Kaspersky, the iPhones malware seeks contact with various command and control servers.
The investigation of the attack technique is still ongoing, but the Kaspersky experts have already been able to determine the general course of infection. Victims received a message via iMessage with an attachment containing a zero-click exploit. Without further interaction, the message exploited a vulnerability that led to privilege escalation code execution, allowing full control over the infected device. Once the attacker had successfully penetrated the device, the message was automatically deleted. In addition, the malware sent private information to other servers, including microphone recordings, instant messenger photos, location data, and other data about a range of other activities by the infected device's owner.
Product portfolio not infected
The attack should provide the attacker with a lot of information. However, the attackers could not access internal data for the development or control of Kaspersky products. The company has already analyzed this. The investigation dubbed Operation Triangulation is ongoing and Kaspersky plans to release more details as soon as possible. There is also a reasonable suspicion that there are other victims of this espionage campaign outside of Kaspersky.
Free malware detection tool
Since many companies are now unsure whether they too have been attacked, Kaspersky offers a free check tool via GitHub. It is therefore publicly accessible and available for macOS, Windows and Linux. Before installing the program, users should backup the device first; and only then install and run the tool. Only the backup that is being analyzed is used for analysis. The only way to completely clean a device is to reset an iPhone to the factory settings, install the new iOS version and set up the device from scratch. However, you should then deactivate iMessage immediately.
The program issues three messages:
- 'DETECTED' confirms that the device has been infected.
- 'SUSPICION' on the other hand, indicates the detection of less clear indicators that suggest a probable infection.
- 'No traces of compromise were identified' is displayed when no Indicators of Compromise (IoCs) were detected at all - and the device is not infected.
“Today we are proud to provide a free public tool that users can use to check if they are affected by the newly discovered advanced threat. With the cross-platform 'triangle_check', users can automatically scan their devices,” comments Igor Kuznetsov, head of the EEMEA unit in the Global Research and Analysis Team (GReAT) at Kaspersky. "We urge the cybersecurity community to join forces in exploring this new APT to build a safer digital world."
Who can develop such malware?
Who has the skills and the means to develop such a perfidious program for a hitherto unknown vulnerability? Already at Pegasus, which was developed by the Israeli company NSO Group, was considered outstanding by experts. Operation Triangulation malware is almost less likely and extremely difficult to detect. Kaspersky had to disassemble and analyze device backups to even find the malware. Time will tell if a state-controlled APT group might be behind the malware.
Editor/sel
Directly to the Kaspersky.com search tool
