Hackers build fraudulent links into Google ads to lure users to dangerous websites.
Check Point Research (CPR), the threat intelligence division of Check Point® Software Technologies Ltd. (NASDAQ: CHKP), a global leader in cyber security solutions, discovered another hacking campaign affecting Google.
Hackers infect Google Ads with scam links. Users don't even have to click on the ads themselves, but instead receive a phishing e-mail that Google Ads uses in the background. Google is particularly interesting because the company is the largest provider of advertising on the Internet.
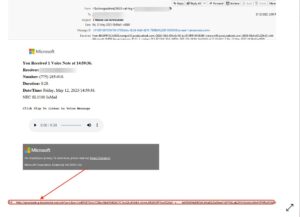
Example of a phishing email
A phishing email arrives in the inbox claiming that the recipient missed a Microsoft voicemail. However, the link does not lead to Microsoft, but to a Google Ad, which in turn leads to the fraudulent website. If the recipient is surprised that the message does not lead to a Microsoft page, they could regain trust because there is a legitimate Google Ads address behind the link. So if the user clicks on the link, he is quickly forwarded to the hacker site via Google Ads in the background.
Use of legitimate sites and services
Once again, the well-known brand name of a company, again Google, is misused in this way to reassure the recipients of the phishing email. This advanced phishing idea is dubbed Business Email Compromise 3.0 (BEC 3.0) by security researchers. It uses legitimate sites and services instead of fake ones. Check Point security researchers expect such attacks to gain popularity and hackers over the course of the year.
The security researchers advise companies and private users to exercise great caution. They also recommend implementing AI-powered IT security solutions that can look out for various indicators, introducing an email security solution that checks documents and files, and a URL security solution that checks and emulates websites.
More at CheckPoint.com
About check point Check Point Software Technologies GmbH (www.checkpoint.com/de) is a leading provider of cybersecurity solutions for public administrations and companies worldwide. The solutions protect customers from cyberattacks with an industry leading detection rate for malware, ransomware and other types of attacks. Check Point offers a multi-level security architecture that protects company information in cloud environments, networks and on mobile devices, as well as the most comprehensive and intuitive “one point of control” security management system. Check Point protects over 100.000 businesses of all sizes.
Matching articles on the topic
More at Sophos.comMatching articles on the topic