
Partnerships, services, customer relationships – no organization operates independently. Contracts, compliances and laws regulate cooperation, but what about security criteria? Cyber attacks on supply chains particularly affect small and medium-sized companies, according to the latest threat report from Sophos.
In the latest Sophos Threat Report: Cybercrime on Main Street The security experts report that in 2023 the Sophos MDR team responded increasingly to cases in which companies were attacked via the so-called supply chain, i.e. the supply chain in business and in the IT infrastructure. In several cases, the vulnerabilities lay in a service provider's remote monitoring and management (RMM) software. The attackers used the RMM agent running on the targeted victim's machines to create new administrative accounts on the attacked network and then used commercial remote desktop, network exploration, and software setup tools. They then successfully installed the LockBit ransomware.
How do you respond to attacks from the service provider?
It is often not easy for SMEs to organize their own cyber security from an economic perspective and in terms of personnel. Once this is achieved, external risks remain. Attacks that exploit trustworthy software and give the option of deactivating endpoint protection are particularly perfidious and often used by criminals. This means: pay particular attention and attention to warnings from the systems that the endpoint protection has been manipulated or deactivated!
The one just released Threat Report: Cybercrime on Main Street documented a number of cases in the last year, in addition to RMM software, in which attackers used vulnerable kernel drivers from older software that still had valid digital signatures. In addition, the experts repeatedly recorded deployments of specially created software that used fraudulently obtained digital signatures - including malicious kernel drivers that were digitally signed via Microsoft's Windows Hardware Compatibility Publisher (WHCP) program - to evade detection by security tools and execute code that disables malware protection.
Manipulation of kernel drivers is a problem
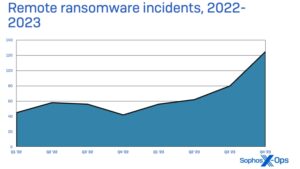
🔎 Data collected over the last two years shows that the proportion of attempted remote ransomware attacks has increased overall - an ongoing problem, with even more momentum in the second half of 2023. (Image: Sophos).
Because kernel drivers work at a very low level within the operating system and are usually loaded before other software when the PC starts, this means that in many cases they are executed before the security software can even start. The digital signatures act as an entry ticket, so to speak. In all versions of Windows since Windows 10 version 1607, kernel drivers must have a valid digital signature, otherwise Windows operating systems with Secure Boot enabled will not load them.
After Sophos notified Microsoft of the discovery of the malicious kernel drivers in December 2022 and Microsoft issued a security advisory, the company revoked a number of certificates of malicious drivers obtained through WHCP in July 2023.
Stolen certificates and manipulated libraries
However, drivers do not necessarily have to be malicious to be exploited. Sophos security specialists have seen several cases where drivers and other libraries from older and even current versions of software products were used by attackers to inject malware into system memory.
Microsoft's own drivers were also used in attacks. A vulnerable version of a driver for Microsoft's Process Explorer utility has been used multiple times by ransomware operators to disable endpoint protection products. In April 2023, Sophos reported on a tool called “AuKill“, which used this driver in several attacks to install Medusa Locker and LockBit ransomware.
Sometimes it is possible to identify vulnerable drivers before they can be exploited. In July, Sophos' code of conduct was triggered by the activity of a driver for another company's security product. The alarm was triggered by a customer's own attack simulation test. The investigation into the incident uncovered three vulnerabilities that were reported to the software manufacturer and subsequently patched.
SMBs can defend themselves against cyber threats
Small and medium-sized companies are just as exposed to cyber threats as global companies and corporations, but do not have the financial and human resources like them. But you can arm yourself:
- consistent training of employees
- Use of multi-factor authentication on all externally facing assets
- constant server and network hygiene (regular patching and updating)
- Migrating difficult-to-manage resources like Microsoft Exchange servers to SaaS email platforms
- Regular vulnerability assessments and penetration testing
About Sophos More than 100 million users in 150 countries trust Sophos. We offer the best protection against complex IT threats and data loss. Our comprehensive security solutions are easy to deploy, use and manage. They offer the lowest total cost of ownership in the industry. Sophos offers award-winning encryption solutions, security solutions for endpoints, networks, mobile devices, email and the web. In addition, there is support from SophosLabs, our worldwide network of our own analysis centers. The Sophos headquarters are in Boston, USA and Oxford, UK.
