
The Russian-linked cybercriminal group TA422 – also known as APT28, Forest Blizzard, Pawn Storm, Fancy Bear and BlueDelta – primarily targets companies in the aerospace, education, financial, technology and manufacturing sectors apart.
The group also primarily targets government agencies in Europe and North America. The attackers primarily relied on phishing campaigns with a large number of messages. This is the result of a new investigation by cybersecurity company Proofpoint, whose security experts have observed a series of phishing activities from TA2023 since March 422. In their campaigns, cybercriminals exploit known vulnerabilities that have not yet been patched by all IT departments, thereby gaining access to their victims' systems.
The most important research results
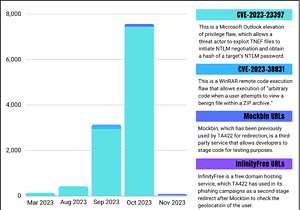
🔎 Registered phishing activities from TA422 or APT28 between March and November 2023 (Image: Proofpoint).
Proofpoint experts observed extensive phishing activity with TA422 targeting aerospace, education, financial, manufacturing, technology, and government organizations in Europe and North America. The group is presumably targeting user data or initiating follow-up activities. ATP 28, for example, also has that immediately Outlook zero-day vulnerability (CVE-2023-23397) exploited.
Since March 2023, Proofpoint has seen a significant increase in emails sent. These activities included exploiting vulnerability CVE-2023-23397, a vulnerability in Microsoft Outlook that allows escalated privileges to be obtained. In late summer 2023, cybercriminals sent more than 10.000 emails attempting to exploit this vulnerability. The perpetrators also took advantage of a WinRAR vulnerability (CVE-2023-38831). The perpetrators posed as geopolitical organizations using the sender addresses and used the BRICS summit and a meeting of the European Parliament as bait in the subject lines.
“The Russian APT group TA422 has continued to abuse known vulnerabilities with extensive email campaigns. “They target government agencies, the defense and aerospace industries, and universities in Europe and North America,” summarizes Greg Lesnewich, Senior Threat Researcher at Proofpoint. “The group’s actions indicate that they are attempting to discover easily infiltrated networks that are of strategic interest. The payloads, tactics, and techniques used in these campaigns demonstrate TA422's definitive move away from the compiled malware that typically secured persistent access to target networks. The goal now appears to be easier, credential-focused access.”
Image1.png
Overview of TA422's activities
Since March 2023, Proofpoint experts have observed that the Russian APT group TA422 is exploiting known vulnerabilities that have not yet been patched by all IT departments to attack a large number of organizations in Europe and North America. The group is assigned by the US intelligence services to the Russian General Staff Directorate (GRU). According to Proofpoint data, while TA422 performed normal targeting activities and used Mockbin and InfinityFree for URL redirection, there was a significant increase in the number of emails exploiting CVE-2023-23397, a vulnerability in Microsoft Outlook.
This included more than 10.000 emails that the attackers sent from a single email provider to defense, aerospace, technology and manufacturing companies, as well as government entities. Smaller message volumes also targeted organizations in higher education, construction and consulting. Proofpoint researchers identified remote TA422 campaigns that attempted to exploit a WinRAR remote execution vulnerability (CVE-2023-38831).
More at Proofpoint.com
About Proofpoint Proofpoint, Inc. is a leading cybersecurity company. The focus for Proofpoint is the protection of employees. Because these mean the greatest capital for a company, but also the greatest risk. With an integrated suite of cloud-based cybersecurity solutions, Proofpoint helps organizations around the world stop targeted threats, protect their data, and educate enterprise IT users about the risks of cyberattacks.
