
Hackers use the ZeroFont phishing trick: using 0-point fonts in emails to make malicious emails appear as if they were securely scanned by security tools in Microsoft Outlook.
Phishing emails that contain fonts with a size of 0 point are not entirely new. While the so-called ZeroFont phishing technique has been used in the past, this is the first time it has been documented in this way. The ISC Sans analyst Jan Kopriva warns that this trick could make a massive difference in the effectiveness of phishing operations and users should be aware of its existence and use in the wild.
This is how ZeroFont phishing works
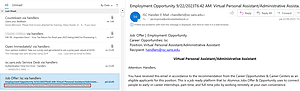
🔎 Actually, the first line of text from the right window should be visible on the left side under the subject - here starting with “Job Offer...” But the text is displayed with a font size of 0 point, which creates a false sense of security (Image: Jan Kopriva).
The trick sounds quite simple, but it has enormous potential: people's curiosity. And it works like this: an email with classic phishing content is sent to a user. The phishing text in the email is visible and all links work. However: the first lines of the phishing email contain an additional short text, which was formatted with a font size of 0 points and is therefore not visible to humans, only to the machine.
For example, the text reads “Mail gscanned and secured by [company name]Advanced Threat Protection” plus a date and time. The line is not visible within the email, but in the quick overview of the emails the first line of text is displayed under the “Subject” because the machine can read 0 point and repeats the text here.
The email looks harmless due to ZeroFont phishing
Many users now think that the email has already been defused by the phishing filter and look at the email. Sometimes they also click on links or even think that the email was marked incorrectly. So the trick worked. Researcher Jan Kopriva shows how the whole thing works in screenshots.
More at ISC.Sans.edu
