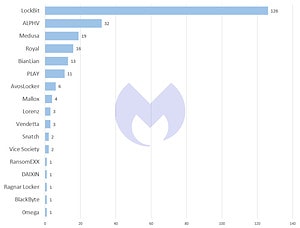
LockBit continues to shape the ransomware scene. The ransomware group again tops the list of groups selling ransomware-as-a-service (RaaS). In February 2023, LockBit reported a total of 126 victims on its leak page, according to analysis by Malwarebytes' threat intelligence team.
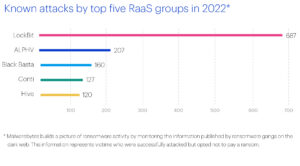
It is not for nothing that the threat intelligence team at Malwarebytes LockBit named in its report "2023 State of Malware’ as one of the top five cyber threats for businesses in 2023. As early as 2022, LockBit consistently proved to be by far the most active ransomware group. According to Malwarebytes, it was responsible for almost a third of all known RaaS attacks in the last year alone. They also account for almost 3,5 times as many attacks as the next largest ransomware group, ALPHV (aka BlackCat). Malwarebytes LockBit was able to attribute a total of 2022 attacks in 687, and only 207 attacks to the ALPHV group.
LockBit: New record for ransom demands
LockBit also breaks records in February 2023 for the amount of ransom demands. While LockBit's highest known ransom demand was $2022 million in 50 - at the time addressed to the German automotive supplier Continental - LockBit demanded $80 million from the British Royal Mail last month.
When Royal Mail denied this request, LockBit released the company's stolen data as well as the chat history that revealed the negotiations between the two parties. This gives interesting insights into the course of professional ransomware negotiations. Malwarebytes suggested that Royal Mail never intended to pay the $80 million ransom. Instead, Malwarebytes noticed clever negotiation tactics on the part of Royal Mail - for example, to play for time in the negotiation or to gain LockBit's trust. A discussion between Mark Stockley, Cybersecurity Evangelist at Malwarebytes, David Ruiz, Senior Privacy Advocate at Malwarebytes, and Zach Hinkle, Social Media Manager at Malwarebytes, also provides more insight into the Royal Mail's negotiations.
After LockBit, ALPHV (aka BlackCat), Medusa, and Royal led the list of known ransomware attacks in February 2023. Malwarebytes' threat intelligence team attributed 32 attacks to ALPHV in February, Medusa 19 attacks, and Royal 16 attacks.
ALPHV and Royal: threat to the healthcare sector
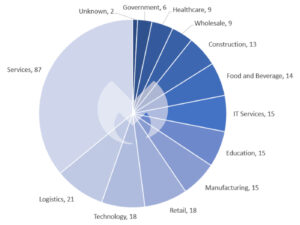
ALPHV and Royal are currently considered to be a major threat to healthcare organizations. The United States Department of Health and Human Services (HHS) even published a detailed report in January 2023 detailing the threat that the two ransomware groups pose to the healthcare sector. However, in February 2023, the two groups appeared to have attacked only one health organization. The ALPHV attack on the Lehigh Valley Health Network in Pennsylvania is known. All of the other victims over the past month have come from other industries, most notably manufacturing, logistics, and services.
Medusa: New activities in February
Medusa ransomware group is the third most active ransomware group as of February 2023 with 20 victims published on their leaks page. Since Malwarebytes introduced the new ransomware group Royal in November 2022, no other new group has attracted attention with such high levels of activity. The victims include, for example, Tonga Communications Corporation (TCC), a state-owned telecommunications company of the Oceanic Kingdom of Tonga, or PetroChina Indonesia, an oil and natural gas company from Indonesia.
United States: Most affected by ransomware attacks
When it comes to the distribution of ransomware attacks by country, the USA is again by far the most common target in February 2023 with 115 attacks. In Europe, the following countries were affected: the United Kingdom with XNUMX attacks, France with XNUMX attacks, Italy with seven attacks and Germany with five attacks.
Industries: targeting the service sector
As in January 2023, the services sector stands out among the industries with 87 attacks in February 2023. The logistics, technology and retail sectors are also conspicuous. Overall, it also seems as if ransomware groups are once again targeting large organizations. For example, in February 2023, the federal agency US Marshals Service (USMS) fell victim to a ransomware attack. The attackers managed to penetrate the agency and obtain sensitive information about employees and people who fled.
While ransomware has often hit local government and municipalities in 2022, attacks on federal agencies remain relatively rare. However, the USMS attack is proof that no organization is safe from ransomware. It is not yet known who is responsible for the attack and whether a ransom demand was made.
More at Malwarebytes.com
Via Malwarebytes Malwarebytes protects home users and businesses from dangerous threats, ransomware and exploits that are undetected by antivirus programs. Malwarebytes completely replaces other antivirus solutions in order to avert modern cybersecurity threats for private users and companies. More than 60.000 companies and millions of users trust Malwarebyte's innovative machine learning solutions and its security researchers to avert emerging threats and eliminate malware that antiquated security solutions fail to detect. You can find more information at www.malwarebytes.com.