Cyber criminals are constantly introducing new techniques and tactics in their phishing attacks to fool victims and bypass security measures. Barracuda has identified three new phishing tactics used by cybercriminals:
Google translate phishing, image phishing, and special character attacks.
After analyzing data on phishing emails in January 2023, Barracuda security researchers have identified three new phishing tactics being used by cybercriminals: attacks that abuse Google Translate links, attacks with image attachments, and attacks using special characters. Safety instructions from Dr. Klaus Gheri, Vice President & General Manager Network Security at Barracuda Networks.
New phishing emails are still rare, but sophisticated
While the volume of these attacks is very small—each attack type accounts for less than 11 percent of the phishing attacks detected by Barracuda's machine learning classifiers—they are widespread, each affecting 15 to XNUMX percent of organizations. The likelihood is therefore high that many companies could encounter one of these malicious messages before the end of the year.
Gateway-based systems offer little to no protection against these types of attacks, and it would take a lot of tuning and control-based rules to protect organizations against them. These attacks are more dynamic in nature, where the payload can change upon delivery, as seen in attacks using Google Translate. Here's a closer look at the three new tactics and best practices that organizations can use to protect against them.
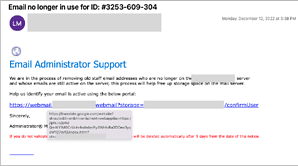
Attacks abusing Google Translate links
Barracuda researchers are seeing an increasing number of email attacks that use Google Translate services to hide malicious URLs. These attacks are commonly referred to as Google translate phishing, translation-based phishing, or translation deception attacks. While only 0,7 percent of the phishing attacks detected by Barracuda's machine learning classifiers used Google Translate links, 13 percent of organizations received this type of phishing email. On average, a company receives about eight of these emails per month.
Google Translate is the most abused service, but the security analysts have also observed similar attacks hidden behind other popular search engines. The attacks are difficult to detect because they contain URLs that point to a legitimate website. As a result, many email filtering technologies go undetected and end up in users' mailboxes.
Attacks using Google Translate help are difficult to detect
In these attacks, cyber criminals use translation services to translate a harmless URL, which they then email to their victims. After email delivery, the attackers modify the payload into malicious content, so gateway-based defenses offer little security. Attacks also use poorly designed HTML pages or an unsupported language to bypass translation. In this case, Google simply returns a link back to the original URL, stating that it is unable to translate the underlying website. Users who mistakenly click the page are redirected to a website controlled by the attacker.
New attacks with image attachments
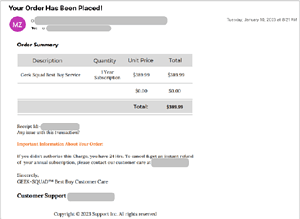
🔎 The use of image-based phishing attacks, here an invoice as an image, is popular because many attacks succeed with it (Image: Barracuda).
Image-based attacks are commonly used by spammers. However, attackers are now also beginning to use images without text in their phishing attacks. These images often contain a callback link or phone number, leading to phishing attacks.
While only 0,2 percent of the phishing attacks detected by Barracuda's machine learning classifiers were image attachments, 11 percent of organizations received this type of phishing email. On average, a company receives about two of these emails per month. Because these attacks contain no text, traditional email gateways go undetected, making it easier for attackers to reach their victims. Most of the image-attachment attacks Barracuda security researchers have uncovered have involved fake invoices, as in the following example:
Image phishing mostly targets businesses
Recently, these types of attacks have come to be known as image phishing or phishing-by-image. They are gaining popularity among criminals, as users are often more willing to trust an image that appears to come from a legitimate source. As email security measures have become more sophisticated, cybercriminals have had to develop new tactics to evade detection. Image-based phishing attacks have proven to be an effective technique to bypass these measures. The use of image-based phishing attacks has increased significantly over the past decade and will likely continue to be a popular tactic for cybercriminals in the future.
Use of special characters in attacks
Hackers often use special characters such as zero-width Unicode code points, punctuation marks, non-Latin script, or spaces to evade detection. While only 0,4 percent of the phishing attacks that Barracuda's machine learning classifiers detected used this type of attack, Barracuda's security researchers found that 15 percent of organizations received phishing emails that misused special characters in this way. On average, a company receives about four of these malicious emails per month.
Do you have a moment?
Take a few minutes for our 2023 user survey and help make B2B-CYBER-SECURITY.de better!You only have to answer 10 questions and you have an immediate chance to win prizes from Kaspersky, ESET and Bitdefender.
Here you go directly to the survey
Detecting these attacks can be very difficult as there are legitimate purposes for using special characters, for example in email signatures. An email security solution that uses machine learning to detect whether the use of special characters is a scam or not is the best way to prevent these threats from reaching users.
Zero-width characters are invisible to readers
The following example shows several zero-width characters used by attackers. These characters are not visible to a user receiving a message, but they are recognizable in the HTML:
These attacks are commonly referred to as "homograph attacks" or simply "no-width space attacks". This type of attack was commonly used in typo-squatting, where an attacker registers a similar-looking domain with special characters to fool recipients. Recently, however, they have been increasingly used within the body of emails to trick recipients into believing they are receiving emails from a legitimate source.
More attacks similar to the new techniques
Punycode Attacks
Like special or zero-width characters, punycode attacks use non-ASCII characters in domain names to create spoofed URLs that mimic legitimate websites and are designed to trick users into entering their username and password or credit card number.
URL spoofing attacks
These attacks use similar domains, which are not necessarily the same as actual legitimate websites or companies. As with Punycode attacks, attackers create login forms that ask users to mistakenly enter their credentials or download rogue files that install ransomware or malware on the local computer.
Typo-Squatting Attacks
This is a fairly common technique against which gateway solutions provide adequate protection. In this case, an attacker might register a domain like yahooo.com to impersonate the real Yahoo! website.
Watering Hole Attacks
In this type of attack, cyber criminals intentionally target a group of users through a compromised website that is known to be visited by their target audience. The attackers inject malicious code into the website and use it to steal login credentials or other sensitive information and even install malware or ransomware.
How companies protect themselves against new phishing attacks
Adequate email protection
It should be ensured that email protection scans and blocks malicious links and attachments. These are often difficult to detect and detection often results in a large number of false positives. The best solutions involve machine learning analysis that examines the image context and subject of the emails and combines them with the sender data to determine whether or not there is an attack.
Employee training
It is important that users are trained to identify and report potential attacks. Phishing attacks are constantly evolving, so it's important to educate users about new types of attacks. Security teams should include examples of these attacks in the organization's phishing simulation campaigns, and encourage users to always double-check before clicking a link or sharing their credentials.
In the event that a malicious email does make it into a user's inbox, security teams should have their remediation tools on hand to quickly identify and remove all instances of a malicious email from the inbox. Automated incident response can help respond quickly before attacks spread throughout the organization. Account takeover protection can also monitor suspicious account activity and alert those responsible if credentials have been compromised.
More at Barracuda.com
Via Barracuda Networks Striving to make the world a safer place, Barracuda believes that every business should have access to cloud-enabled, enterprise-wide security solutions that are easy to purchase, implement and use. Barracuda protects email, networks, data and applications with innovative solutions that grow and adapt as the customer journey progresses. More than 150.000 companies worldwide trust Barracuda to help them focus on growing their business. For more information, visit www.barracuda.com.