DataGuard releases “Information Security-as-a-Service” solution. The combination of a digital web platform and personal support from certified experts enables companies to effectively implement their information security goals.
In this way, DataGuard supports organizations of all sizes and industries in laying the foundation for a sustainable growth strategy, increased customer trust and more security.
All-round solution for information security
Established in the field of data protection consulting and implementation and with locations in Munich, Berlin and London, DataGuard is now publishing the ideal addition to its portfolio: a comprehensive all-round solution for information security. What is special about it is the combination of personal and strategic advice from interdisciplinary, certified industry experts and an intuitive, digital web platform that serves as an information security management system (ISMS) and for the digitization of information security.
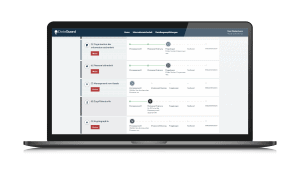
Objective, documentation, asset and risk assessment - information security as a service (Photo. DataGuard).
The planning, implementation and maintenance of the ISMS can be divided into individual process steps, which are digitally recorded in the DataGuard platform and clearly visible on a dashboard. The features range from structured questionnaires and downloadable templates to the recording of assets and the associated risk assessments to auditable documentation.
Both the platform and the personal advice are specifically tailored to the respective customer. DataGuard supports you in the context of intensive advice or as an external information security officer. DataGuard guides companies step by step through all information security management processes, gives clear recommendations for action, calculates risks and supports them in preparing for information security certifications and assessments such as ISO 27001 or TISAX® as well as in training the workforce. The main goals include the confidentiality, integrity and availability of information.
4 steps to effective information security management
- 1. Objective, documentation, asset and risk assessment
- 2. Validation, KPIs and documentation
- 3. Training and internal audit according to ISO 27001
- 4. Support during the external audit
DataGuard supports customers in a targeted manner in preparing for an initial certification according to ISO 27001 by an external auditor and participates on behalf of the customer if requested.
www.dataguard.de
About DataGuard
DataGuard offers a digital web platform for data protection and information security. More than 1.500 customers already rely on the "Data Protection-as-a-Service" and "Information Security-as-a-Service" complete solutions to comply with current data protection regulations (e.g. DSGVO) or to obtain and hold relevant certifications (e.g ISO 27001, TISAX®). With over 150 employees in Munich, Berlin and London, DataGuard enables its customers to seamlessly integrate data protection and information security into their business processes. The result: watertight compliance, efficient risk minimization and added value through trust and transparency. More information at www.dataguard.de or on LinkedIn and Twitter.
