Check Point Research has discovered a software service that has been helping hackers bypass EDR (Endpoint Detection & Response) protection for over six years. The software service serves as a door opener for Emotet, REvil, Maze and other malware.
Beneficiaries of the TrickGate service include well-known malware such as Cerber, Trickbot, Maze, Emotet, REvil, Cobalt Strike, AZORult, Formbook, AgentTesla - a colorful parade of top malware Check Point releases monthly.
Old service undermines EDR
TrickGate is transformative and changes regularly, which helped keep it undiscovered for years. By using TrickGate, malicious actors can proliferate their malware more easily and with fewer consequences for themselves.
TrickGate has managed to fly under the radar for years because it changes regularly. While the wrapper of the packer that compresses the data changed over time, the main building blocks of the TrickGate shell code are still used.
Manufacturing victims
According to the telemetry data, the hackers using TrickGate primarily target manufacturing, but also target educational, healthcare, financial, and commercial institutions. The attacks are spread across the world, with an increased concentration in Taiwan and Turkey.
Encryption of the malicious program makes detection more difficult
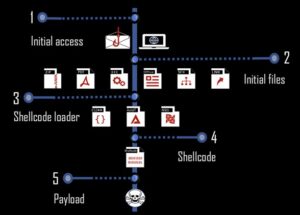
There are many forms of attack flow. The shellcode is the core of the TrickGate packer. It is responsible for deciphering the malicious instructions and code and secretly injecting it into new processes. The malicious program is encrypted and then packaged with a special routine that can be used to bypass the protected system, which is why the security solutions cannot detect the payload either statically or at runtime.
Who is behind TrickGate?
Check Point Research has not been able to determine a clear affiliation. Based on the customers they serve, the security researchers assume that it is a Russian-speaking underground gang.
More at CheckPoint.com
About check point Check Point Software Technologies GmbH (www.checkpoint.com/de) is a leading provider of cybersecurity solutions for public administrations and companies worldwide. The solutions protect customers from cyberattacks with an industry leading detection rate for malware, ransomware and other types of attacks. Check Point offers a multi-level security architecture that protects company information in cloud environments, networks and on mobile devices, as well as the most comprehensive and intuitive “one point of control” security management system. Check Point protects over 100.000 businesses of all sizes.