Emotet continues to be more than active: in March, attacks using Emotet more than tripled. Germany is among the most attacked countries worldwide. The biggest problem: Emotet spreads itself via spam.
Emotet, the world's most dangerous malware according to Europol [1], is currently "celebrating" a sad comeback a year after it was destroyed. According to Kaspersky telemetry, the number of attacks via this botnet tripled from February to March 2022 alone [2]. 2,2 percent of the companies and private individuals attacked in the first quarter came from Germany, which is one of the top 10 countries affected. This growth indicates that, for the first time since their comeback in November 2021, the threat actors behind the botnet have taken concrete steps to significantly ramp up their malicious activity again.
Emotet: Both botnet and malware
Emotet is both a botnet and malware and was first discovered in 2014. Originally intended to spy on access data for online banking, it has developed into a dangerous botnet through numerous modifications [3]. At the beginning of 2021, Emotet was crushed through joint efforts by international investigative authorities. However, the botnet reappeared in November 2021 and has been increasing its activities ever since. It first spread via the banking Trojan Trickbot [4]; now it is able to spread on its own.
Kaspersky telemetry data shows an increase in the number of victims from 2.843 in February 2022 to 9.086 in March. Accordingly, the number of registered attacks almost tripled during this period: from 16.897 in February to 48.597 in March.
Emotet spreads itself via spam
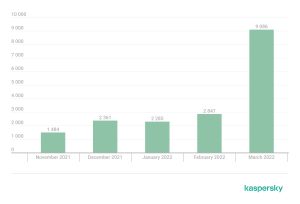
Since Emotet's return in November 2021, we have observed its activity gradually increasing. While it was still 2022 in February 2.847, it had already shot up to 2022 in March 9.086 – more than three times as much (Image: Kaspersky).
Emotet infection typically occurs via spam emails with Microsoft Office attachments that contain malicious macros. A PowerShell command downloads a loader. Controlled by the command and control server, it then downloads other malicious modules with different functionalities onto the infected device. Kaspersky researchers were able to identify and analyze 10 out of 16 modules, most of which have already been used by Emotet in one form or another in the past.
The current version of Emotet can automatically generate spam, which spreads further in the network from the infected devices. Emails and email addresses are extracted from Thunderbird and Outlook applications and passwords of popular web browsers such as Internet Explorer, Mozilla Firefox, Google Chrome, Safari and Opera are collected to recover the email account data of various E - Capture mail clients.
New momentum at Emotet
“Emotet was a highly developed network that afflicted many companies worldwide. Its dismantling thus represented a significant step towards reducing global threats to corporate networks and eliminated Emotet from the list of the top ten cyber threats for almost a year,” concludes Alexey Shulmin, Security Researcher at Kaspersky. “Although the current attack numbers are not comparable to previous Emotet activities, the renewed momentum points to significantly increased activities by botnet operators. There is a high probability that Emotet will become even more widespread in the coming months.”
Kaspersky recommendations for businesses to protect against Emotet and similar botnets
- Keep an eye on the latest developments on Emotet, for example via the Kaspersky Resource Center [5].
- Do not download attachments or click on suspicious links in spam emails. Verify suspicious emails by calling back the sender. Under no circumstances should you comply with the request to run macros, but delete the corresponding files immediately.
- Only use online banking with multi-factor authentication.
- Companies should also conduct regular employee training such as Kaspersky Security Awareness [7] on Internet threats and test their effectiveness using simulated phishing attacks.
Kaspersky has published a documentary about combating the Emotet botnet on its Tomorrow Unlocked YouTube channel [8].
More at Kaspersky.com
About Kaspersky Kaspersky is an international cybersecurity company founded in 1997. Kaspersky's in-depth threat intelligence and security expertise serve as the basis for innovative security solutions and services to protect companies, critical infrastructures, governments and private users worldwide. The company's comprehensive security portfolio includes leading endpoint protection as well as a range of specialized security solutions and services to defend against complex and evolving cyber threats. Kaspersky technologies protect over 400 million users and 250.000 corporate customers. More information about Kaspersky can be found at www.kaspersky.com/
[1] https://www.europol.europa.eu/media-press/newsroom/news/world%E2%80%99s-most-dangerous-malware-emotet-disrupted-through-global-action
[2] https://securelist.com/emotet-modules-and-recent-attacks/106290/
[3] https://securelist.com/the-chronicles-of-emotet/99660/
[4] https://www.kaspersky.com/blog/trickbot-new-tricks/42622/
[5] https://www.kaspersky.com/resource-center/threats
[6] https://www.kaspersky.de/internet-security
[7] https://www.kaspersky.de/enterprise-security/security-awareness
[8] https://www.youtube.com/watch?v=s3o3qOipHhk
Matching articles on the topic
