Check Point Research (CPR) security researchers found that cyber criminals use Telegram bots to bypass ChatGPT restrictions on underground forums. The bots use OpenAI's API to create malicious emails or code.
Chat bot makers currently give up to 20 free queries, but then charge $5,50 for every 100 queries. CPR therefore warns of ongoing efforts by cybercriminals to circumvent ChatGPT's restrictions in order to use OpenAI for malicious purposes.
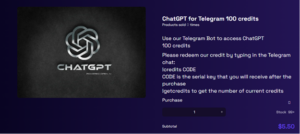
Telegram ChatGPT Bot as a Service
CPR found advertisements for Telegram bots on underground forums. The bots leverage OpenAI's API to allow a threat actor to craft malicious emails or code. The bot's creators give up to 20 free queries, but then charge $5,50 for every 100 queries.
“OpenAI has created barriers and restrictions as part of its Content Policy to prevent the creation of malicious content on its platform. However, we see cyber criminals circumventing ChatGPT restrictions. The underground forums are actively chatting about how to use the OpenAI API to bypass the barriers and limitations of ChatGPT. This is mostly done by creating Telegram bots that use the API.
ChatGPT: Abuse possible via API
These bots are promoted on hacking forums to increase their exposure. The current version of the OpenAI API is used by external applications and has very few anti-abuse measures. Therefore, it is possible to create malicious content such as phishing emails and malware code without the restrictions or barriers that ChatGPT has put in place on its interface. We are currently seeing ongoing efforts by cybercriminals to find ways to bypass ChatGPT restrictions.” said Sergey Shykevich, threat group manager at Check Point Software.
More at CheckPoint.com
About check point Check Point Software Technologies GmbH (www.checkpoint.com/de) is a leading provider of cybersecurity solutions for public administrations and companies worldwide. The solutions protect customers from cyberattacks with an industry leading detection rate for malware, ransomware and other types of attacks. Check Point offers a multi-level security architecture that protects company information in cloud environments, networks and on mobile devices, as well as the most comprehensive and intuitive “one point of control” security management system. Check Point protects over 100.000 businesses of all sizes.