
It's still a cyber attack in the laboratory: Israeli researchers installed malware on a PC and then used the electromagnetic waves generated by a PC power supply to transfer some data to a remote smartphone behind a wall.
Israeli researchers have studied a new attack method called the COVID-Bit. It uses the electromagnetic waves of a device, such as a PC, to transmit data from devices that are isolated from the Internet (air-gap systems) over a distance of at least two meters. There they can be captured by a receiver with a smartphone – even behind a wall. How to have the researchers set out in a freely available technical PDF file.
Tapped devices without internet access
The COVID-bit attack was developed by Ben-Gurion University researcher Mordechai Guri, who has studied multiple methods to steal sensitive data from air-gap systems. It is not primarily about the attack, but about recognizing what is possible and how to defend against it.
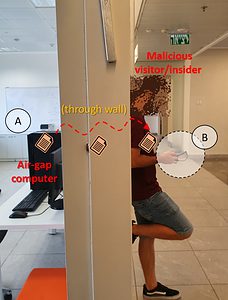
🔎 This is how researchers attacked the Air Gap system in an experiment (Image: Ben-Gurion University of the Negev).
So-called air gap systems are usually found in high-risk environments such as energy infrastructure, government and weapons control units. These systems are always disconnected from the Internet or have no access at all. However, for the researched attack to work, malware must be installed on the PC or system. That sounds far-fetched but was the case with Stuxnet, for example. The worm so misdirected Iran's uranium enrichment centrifuge control systems that they were destroyed.
Low data transfer rates
The first results show very low data transfer rates, but these are sufficient. In addition, the research was more about demonstrating the feasibility of this attack. To transmit the data in the COVID-bit attack, the researchers created a malware program that regulates the CPU load and thus the core frequency in a specific way to make the power supplies on air-gap computers emit electromagnetic radiation broadcast on a low frequency band.
According to the researchers, a proper defense against such attacks is very difficult, since the CPU and power supply frequencies would have to be monitored on the air gap systems.
More at Sophos.com
