As early as May 24, 2022, Cisco noticed that an employee's login data had been fished out and misused. While Cisco has commented on the attack, it has not provided any information about the stolen data. The Yanluowang ransomware gang claims to have captured 2,8 GB of data and is apparently offering it for sale.
On May 24, 2022, Cisco became aware of a potential compromise. Since then, Cisco Security Incident Response (CSIRT) and Cisco Talos have been working to resolve the issue. During the investigation, it was discovered that a Cisco employee's credentials were compromised after an attacker gained control of a personal Google account used to sync credentials stored in the victim's browser.
Successful voice phishing attacks
The attacker ran a series of sophisticated voice phishing attacks under the guise of various trusted organizations that attempted to convince the victim to accept attacker-initiated push notifications using multi-factor authentication (MFA). The attacker eventually managed to achieve an MFA push acceptance that granted them access to VPN in the context of the targeted user.
CSIRT and Talos investigated the event and found no evidence that the attacker gained access to critical internal systems and was able to extract important information. After gaining initial access, the threat actor performed a variety of activities to maintain access, minimize forensic artifacts, and increase its access to systems within the environment.
Attackers detected and locked out
According to Cisco, the threat actor was successfully removed from the environment. However, he appears to have shown persistence by repeatedly attempting to regain access in the weeks following the attack; However, these attempts were unsuccessful. Cisco estimates with medium to high confidence that this attack was performed by an attacker previously identified as an Initial Access Broker (IAB) with ties to the UNC2447 cybercrime gang, the Lapsus$ threat actors group, and the Yanluowang ransomware operators. Cisco lists more information on its Cisco Response page.
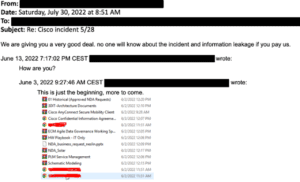
The page Bleeping Computer however, reports that the Yanluowang ransomware gang stole 2,8 GB of data and is now offering it for sale on the dark web. Some screenshots should prove this. Furthermore, the Yanluowang group posted on their leak page on 10.08.22/XNUMX/XNUMX that the time had expired and that “there will be interesting things on their page from this point onwards”.
More at Cisco.com