Palo Alto Networks' security research team evaluated more than 100 companies across multiple industries to map their unmanaged attack surfaces. The results have been compiled in the current Attack Surface Threat Report.
Seasoned security professionals know that while zero-days make the headlines, the real problems arise from the dozens of small decisions that are made every day in an organization. Even a single accidental misconfiguration can create a weak point in the defense.
Oversights and misconfigurations targeted
Opportunistic attackers are increasingly targeting these oversights and misconfigurations as it has become easy and inexpensive to find vulnerabilities, exposures, or other unknown open doors. Even less skilled attackers can set up a scanning infrastructure to roughly scour the Internet and discover compromiseable objects. Some may even try to crack this vulnerability, but far more enterprising attackers sell this scan data to bidders on the dark web, who can then launch more sophisticated attacks. It is therefore a great advantage for defenders if they know the attack surface of an attacker.
For a more in-depth analysis, the researchers examined a sample of CVE (Critical Vulnerabilities and Exposure) data from January to February 2022 for which exploits were already known to be active and were highlighted in key cybersecurity recommendations from US federal agencies.
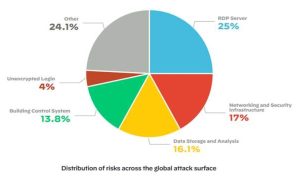
These are some of the key findings from Palo Alto Networks' 2022 ASM Threat Report, which is based on observable data from more than 100 companies rather than self-reported surveys:
- The cloud continues to be a security nightmare: Almost 80 percent of all problems observed on the global attack surface took place in the cloud. While simple, cloud deployments lead to numerous unintended attacks due to misconfigurations and shadow IT.
- Low-hanging fruits continue to hang: Non-zero-day threats are everywhere. Nearly one in four issues the researchers found on the attack surface was related to an unprotected RDP server, which has become the preferred gateway for ransomware. The Xpanse investigation also uncovered over 700 unencrypted login pages for various IT services that were unencrypted and publicly accessible. Nearly 3.000 database storage and analysis systems and over 2.500 critical building control systems (BCS) were also accessible via the public internet.
- End-of-life software = end-of-life for security: 30 percent of organizations were using end-of-life (EOL) versions of software affected by CVEs that had known active exploits and were listed in US government cybersecurity advisories.
- The uncontrolled attack surface is increasing: The researchers also found that while several companies had a large number of active issues that they fought within a month, they were never truly certain. These companies remained vulnerable throughout the month as their unmanaged attack surface continued to grow while other security issues were addressed.
- Persistent, complex, but unique: Xpanse research found that while each industry's attack surface is unique, vulnerabilities remain. For example, nearly 23 percent of all problems in the utilities and energy sector were due to compromised building control systems. Nearly 50 percent of all professional and legal service issues involved data storage systems and unencrypted logins exposed to the public Internet. This put intellectual property, important customer data and other highly sensitive information at risk.
find vulnerabilities
If security teams don't know where the vulnerabilities are, it's impossible to ensure that the problems are fixed. For many organizations, the cloud and RDP will be constant targets, but the constellation of risks and vulnerabilities on your attack surface will only continue to grow as attack surfaces become more complex.
Attackers benefit from the complexity and ever-changing attack surfaces because they can search the entire Internet for these vulnerabilities. With an attacker's perspective, organizations can identify problems and prioritize them in order to fix them. It also means that focusing on metrics like Mean Time To Detect (MTTD) and Mean Time to Respond (MTTR) is inherently flawed.
MTTD and MTTR for security breaches
In the event of a security breach, MTTD and MTTR are acceptable, but Palo Alto Networks believes security should focus on doing everything possible to prevent security breaches before they happen. This means that organizations should place more emphasis on Meant Time To Inventory (MTTI) as it is impossible to protect unknown assets from unknown risks.
Modern attack surfaces are dynamic. Without a clear overview that is constantly updated, it is all too easy to have persistent vulnerabilities and unmanaged assets. Security professionals can only be as good as the data they have at their disposal. Palo Alto Networks believes a solid foundation of continuous detection and monitoring ensures organizations can keep pace with modern, dynamic attack surfaces to find, prioritize, and mitigate vulnerabilities as they emerge.
More at PaloAltoNetworks.com
About Palo Alto Networks Palo Alto Networks, the global leader in cybersecurity solutions, is shaping the cloud-based future with technologies that transform the way people and businesses work. Our mission is to be the preferred cybersecurity partner and protect our digital way of life. We help you address the world's biggest security challenges with continuous innovation leveraging the latest breakthroughs in artificial intelligence, analytics, automation, and orchestration. By delivering an integrated platform and empowering a growing ecosystem of partners, we are the leaders in protecting tens of thousands of businesses across clouds, networks and mobile devices. Our vision is a world where every day is safer than the one before.