
Many sources indicate that the Subway company was the victim of a cyberattack by LockBit. The operator Subway is currently not issuing a statement on this. There is still a countdown until February 2, 2024 on Lockbit's leak page.
What data could be captured from Subway that isn't already published? This question should be clarified after February 2, 2024, after the countdown on LockBit's leak page has expired. The fast food chain Subway is listed as a victim of data theft. According to some other media, Subway denies the hack by LockBit and does not comment further.
LockBit claims to have stolen several 100 GB of data
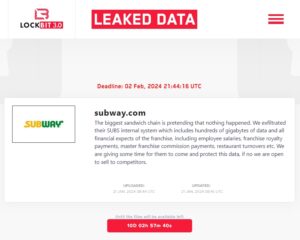
🔎 On its leak page, LockBit claims the theft of hundreds of gigabytes of data from Subway (Image: B2B-CS).
LockBit is actually not known for declaring extortion online and then not getting anything. However, of course, no one yet knows how confidential the data is or whether it is just a harmless document. The text published by LockBit reads somewhat frighteningly:
“The largest sandwich chain acts as if nothing happened. We have exfiltrated their internal SUBS system, which contains hundreds of gigabytes of data and all of the franchise system's financial data, including employee salaries, franchise license payments, master franchise commission payments, restaurant sales, etc. We are giving them some time to access this data protect, otherwise we are open to selling to competitors.”
Hundreds of gigabytes of data sounds like a lot. If that is true, then Subway's systems are not particularly protected if they have not noticed and stopped such a large amount of data being withdrawn from the network. But so far it's all just speculation - we'll know more after February 2, 2024.
Double extortion method
A comment from Richard Werner, Business Consultant at Trend Micro.
“Lockbit is one of the most dangerous RaaS (Ransomware-as-a-Service) groups currently in existence. Their victims are primarily found in the USA and Europe. Around 70 percent of them consist of small and medium-sized companies (< 500 employees). Between 500 and 800 individual victims can be identified every six months. However, it should be noted that we only know the victims who initially refuse to pay. A few background information about the method.
Globally, only about a seventh of companies (~14 percent) appear to pay due to double extortion. This doesn't even have to be related to this method, but can also mean that the victim is actually paying for the decryption and therefore the extortion with the data is withdrawn.
But the large amount of stolen data that is being discussed, as here at Subway, is ultimately a selling point. Speculation about possible scandals or valuable content is primarily intended to identify prospective buyers. Because that’s how money is made if the victim doesn’t pay – and that’s also recommended.”

