More than a third of German managers have shared their password with someone outside their own company. A recent study shows how relaxed managers are about cybersecurity.
Security provider Ivanti has presented the results of the Executive Security Spotlight Report. The study deals with security behavior specifically at the C-level in the company. Although this group of people is constantly in the focus of spear phishing or whaling actors, executives are surprisingly relaxed when it comes to cybersecurity.
Managers are often the target of threats
The main sticking point: Due to their management tasks, they are often endowed with extensive access rights. And where they lack permissions, they circumvent security requirements. The Ivanti study is part of a series of surveys on employee safety behavior. The company surveyed 6.500 executives, cybersecurity experts and office workers worldwide.
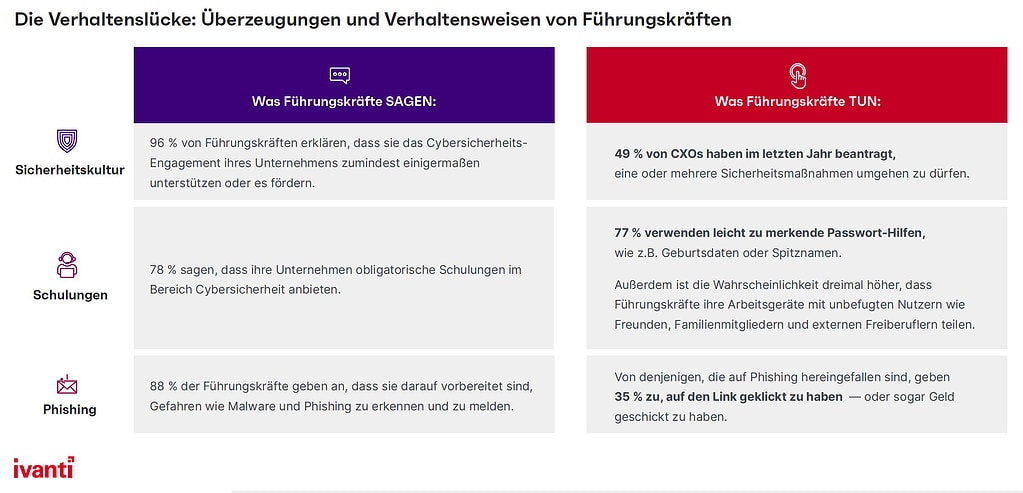
Top executives often have unhindered access to corporate data sources and connected devices. However, they are the group of employees most often targeted by threat actors. They are well aware of their exposed position: 96% of them say that they support and are committed to their company's cybersecurity mission.
But the reality is different. According to the study results, every second top decision-maker (49%) had circumvented one or more security measures in the past year. This pattern runs through the entire survey: Be it due to a lack of time to go through specific processes or a feeling of special status: managers tend to behave more riskily than the rest of the workforce
Key findings of the report:
- One in five managers has already shared their work password with someone outside the company - in Germany even one in three CXOs (37%).
- Three quarters (77%) use easy-to-remember passwords that include birthdays or pet names, among other things.
- CXOs are three times more likely to share work devices with unauthorized users such as friends or family than any other employee.
- Last year, one in three managers accessed work files and data for which they did not have authorization - one in two in Germany.
- One in four (24%) still uses the same password that they were originally given. For office workers, this figure is only 14%.
Managers use external support more often
The Ivanti study also sheds light on the sometimes critical collaboration between managers and the security teams: In contrast to the rest of the workforce, managers are twice as likely to say that they found their interactions with the security department to be “unpleasant” or “embarrassing”, for example when they have expressed safety concerns. This results in executives four times more likely to use external, unapproved technical support.
The results highlight the need for trusting collaboration between security teams and executives: “When executives are willing to trade security for ease of use, they underestimate that they are a lucrative target for threat actors,” explains Daniel Spicer, chief security officer at Ivanti. “The challenge for security leaders is to demand the support of the company in carrying out cyber tasks - especially from the leadership team. Because not all members of the management level respect cyber hygiene.”
Measures to close the leadership behavior gap include audits, prioritizing remediation actions for the most common risks, conducting “game-based” security training, and implementing so-called “white glove” security programs.
More at Ivanti.com
About Ivanti The strength of unified IT. Ivanti connects IT with security operations in the company in order to better control and secure the digital workplace. We identify IT assets on PCs, mobile devices, virtualized infrastructures or in the data center - regardless of whether they are hidden on-premise or in the cloud. Ivanti improves the provision of IT services and reduces risks in the company on the basis of specialist knowledge and automated processes. By using modern technologies in the warehouse and across the entire supply chain, Ivanti helps companies improve their ability to deliver - without changing the backend systems.
Matching articles on the topic