Security researchers at SophosLabs have been investigating the current activities of the reactivated Emotet botnet. They describe how Emotet currently uses CFF, a coding technique used by the botnet's malware to camouflage and hide from security measures.
Emotet has been one of the most professional and long-lived cybercrime services and malware infections in the threat landscape. The botnet became notorious shortly after its debut in 2014 and was stopped in January 2021 by a multinational law enforcement operation that grounded its activities for almost a year. Finally, in November 2021, the botnet resurfaced and reappeared on Sophos' radar.
Emotet: Back on the radar
"After a nearly year-long law enforcement hiatus, the infamous Emotet botnet is back on the rise, as evidenced by SophosLabs' sandboxes and monitoring systems," said Andreas Klopsch, security researcher at SophosLabs.
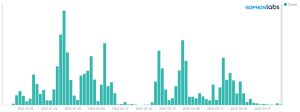
“The bar chart above shows the emergence of Emotet detected in Sophos sandbox systems in Q2022 XNUMX. As can be seen from the chart, we receive multiple Emotet submissions daily; we assume that the recurring major spikes are large-scale campaigns. Emotet is mainly distributed via email spam, and more malicious emails naturally lead to more sandbox submissions.
Also, the research team noticed that Emotet often uses CFF as an accelerator to slow down defenses; a technique used since 2020.
Obfuscation as a tactic
“CFF is a well-known obfuscation technique used to mask malware's intent, making it difficult for defenders to understand and protect against attacks. The process of removing this obfuscation technique is called 'unflattening'. Our research team at SophosLabs has managed to uncover most of the obfuscated functionality and broken several additional layers of obfuscation. This allows us to dig deeper into the internal workings of Emotet. This enables companies to have better detection and a faster response time in the event of an Emotet attack,” says Andreas Klopsch.
Sophos has also released a tool on GitHub to help defenders unflatte stacks of CFF layers in an Emotet attack and to unveil.
More at Sophos.com
About Sophos More than 100 million users in 150 countries trust Sophos. We offer the best protection against complex IT threats and data loss. Our comprehensive security solutions are easy to deploy, use and manage. They offer the lowest total cost of ownership in the industry. Sophos offers award-winning encryption solutions, security solutions for endpoints, networks, mobile devices, email and the web. In addition, there is support from SophosLabs, our worldwide network of our own analysis centers. The Sophos headquarters are in Boston, USA and Oxford, UK.