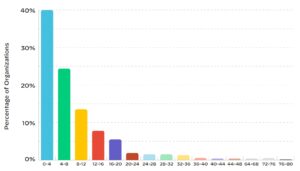
The Cloud Threat Report Volume 7 reveals: After an alert for a security team, attackers have up to 40 days to carry out their attack in 4 percent of cases. Attackers are helped by the 60 percent unpatched high or critical vulnerabilities.
The cloud attack surface is as dynamic as the cloud itself. As organizations around the world increasingly share, store, and manage data in the cloud, the attack surface for businesses is expanding exponentially. This expansion often happens in unknown, overlooked, or poorly secured ways. For attackers, every workload in the cloud represents an opportunity, and without proper management, organizations are exposed to myriad risks.
Target of attack: Everyday problems in the cloud
While previous reports have focused on a single threat (e.g., identity access management, supply chain attacks, and container security), Unit 42 Cloud Threat Report Volume 7 “Navigating the Expanding Attack Surface” addresses a larger, broader problem: attackers are become adept at exploiting common, everyday problems in the cloud. These problems include misconfigurations, weak credentials, lack of authentication, unpatched vulnerabilities, and malicious open source software (OSS) packages.
The report provides a breakdown of two different real-world instances of cloud attacks observed by Unit 42 in 2022. After anonymizing and de-identifying victims, the researchers reveal how attackers exploited sensitive data leaked on the dark web and the business disruption caused by ransomware.
Important findings of the report
- On average, it takes security teams 145 hours (about six days) to resolve a security incident. 60 percent of companies take more than four days to resolve security issues.
- In most enterprise cloud environments, 80 percent of alarms are triggered by just XNUMX percent of security policies.
- 63 percent of codebases in production have unpatched vulnerabilities rated high or critical (CVSS >= 7.0)
- 76 percent of organizations do not enforce MFA for console users, while 58 percent of organizations do not enforce MFA for root/admin users.
Common monitoring measures in the cloud
Based on extensive data collected in 2022, the report examines real-world security breaches that affected medium-sized and large organizations. He describes the issues observed in thousands of multi-cloud environments and analyzes the impact of OSS vulnerabilities on the cloud. Specifically, the researchers analyzed the workloads across 210.000 cloud accounts across 1.300 different companies. As many companies now have multiple cloud implementations, the vulnerabilities are increasingly being targeted by attackers.
Do you have a moment?
Take a few minutes for our 2023 user survey and help make B2B-CYBER-SECURITY.de better!You only have to answer 10 questions and you have an immediate chance to win prizes from Kaspersky, ESET and Bitdefender.
Here you go directly to the survey
While user errors such as insecure configurations remain the main problem, Unit 42 researchers have also identified issues stemming from the ready-made templates and default configurations provided by cloud service providers (CSPs). While these settings and features are convenient and make it easier to adopt new technologies, they do not put users in the safest place to start.
Exemplary results:
- 76 percent of organizations are not enforcing MFA for console users.
- Sensitive data was found in 63 percent of publicly accessible storage buckets.
Cloud: risks of open source software (OSS)
Open source software was one of the driving forces behind the cloud revolution. However, the increasing use of OSS in the cloud also increases complexity - and with it the likelihood of obsolete or discontinued software, malicious content and slower patching cycles. This makes it the responsibility of end users to validate the OSS before integrating it into applications. This task is especially difficult when companies have to manage numerous projects, all of which depend on potentially thousands of OSSs.
Recommendations: Make life difficult for attackers
Enterprises should expect the attack surface for cloud-native applications to continue to grow as attackers find increasingly creative ways to attack the misconfiguration of cloud infrastructure, APIs, and the software supply chain itself.
To protect against these threats, the report provides practical guidance on closing the cloud security gaps, such as:
An automated backup process should be in place for all cloud workloads that would disrupt business operations in the event of a failure. Backups should be stored in protected locations isolated from the production environment across multiple geographic locations to avoid a single point of failure. All organizations should have business continuity and disaster recovery (BC/DR) plans that include the process of restoring from backups.
In addition, the researchers predict that the industry will move away from point security solutions towards cloud-native application protection platforms (CNAPPs) that offer a full spectrum of capabilities across the entire application development lifecycle. Gartner backs up this claim that there will be a significant uptick in CNAPP adoption, reporting a 70% increase in customer inquiries about CNAPPs between 2021 and 2022.
More at PaloAltoNetworks.com
About Palo Alto Networks Palo Alto Networks, the global leader in cybersecurity solutions, is shaping the cloud-based future with technologies that transform the way people and businesses work. Our mission is to be the preferred cybersecurity partner and protect our digital way of life. We help you address the world's biggest security challenges with continuous innovation leveraging the latest breakthroughs in artificial intelligence, analytics, automation, and orchestration. By delivering an integrated platform and empowering a growing ecosystem of partners, we are the leaders in protecting tens of thousands of businesses across clouds, networks and mobile devices. Our vision is a world where every day is safer than the one before.