Sophos registers the scans for Log4j vulnerabilities worldwide and the countries from which many exploits come: China and Russia. The findings show two heat maps. Sean Gallagher, Senior Threat Researcher at Sophos
“Sophos continues to monitor scans for Log4j vulnerabilities. In the past, we've seen large spikes and then sharp drops in such scans and exploit attempts. In the case of Log4j, we didn't see a drop, but rather daily scans and access attempts from a globally distributed infrastructure. We expect this high level of activity to continue as the vulnerability is multifaceted and requires extensive patching.
As already indicated, in some cases a request comes from an IP address in a geographic region, with embedded URLs for Log4j connecting to servers elsewhere - sometimes to multiple different servers. And while some of these requests are harmless testing or 'research' by penetration testers and other security researchers, a larger proportion are malicious.”
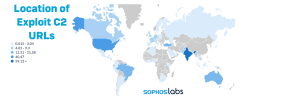
“For example, Sophos telemetry shows that 59% of exploit attempts are aimed at connecting Log4j to Internet addresses in India. More than 40% of the exploit attempts try to link Log4j to Internet addresses in the USA. ”The scan attempts in Germany account for around 11% of the cases registered by SophosLabs worldwide, but also include activities by security companies .
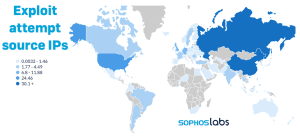
“However, the exploit attempts themselves come predominantly from China and Russia, with most of these attempts arguably cybercrime-related. A server in Russia connected to the Kinsing cryptocoin-mining botnet is responsible for more than 10% of exploit attempts observed by Sophos — more than 33% of all traffic originating in Russia.” When it comes to exploits, Germany is at 2%.
Sophos also publishes the detailed article “Logjam: Log4j exploit attempts continue in globally distributed scans, attacks”. It describes the new Log4j scanning and exploit activity shown above and provides the “Location of Exploit C2 URLs” and “Exploit Attempt Source IPs” heatmaps.
More at Sophos.com
About Sophos More than 100 million users in 150 countries trust Sophos. We offer the best protection against complex IT threats and data loss. Our comprehensive security solutions are easy to deploy, use and manage. They offer the lowest total cost of ownership in the industry. Sophos offers award-winning encryption solutions, security solutions for endpoints, networks, mobile devices, email and the web. In addition, there is support from SophosLabs, our worldwide network of our own analysis centers. The Sophos headquarters are in Boston, USA and Oxford, UK.