
Microsoft has fallen victim to its own Azure Active Directory – AAD configuration challenges. Due to the misconfiguration, experts managed to add malicious code to some Bing search results, which exposed Microsoft 365 users.
Wiz Research experts found the configuration errors and exploited them for testing. Microsoft rewarded the experts with a BugBounty and fixed the bugs immediately. What happened? The experts describe the incident:
Manipulated Bing search results including malicious code
“These applications allowed us to view and modify various types of sensitive Microsoft data. In one particular case, we were able to manipulate search results on Bing.com and perform XSS attacks on Bing users, potentially exposing customer Office 365 data such as emails, chats and documents.”
Azure Active Directory (AAD)
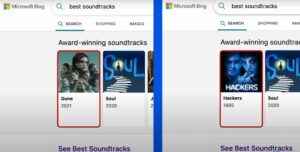
🔎 With the vulnerability, the WIZ researchers were able to change the search result in Bing (Image: Wiz Research).
Microsoft offers its own SSO service in AAD, one of the most common authentication mechanisms for apps built in Azure App Services or Azure Functions. AAD offers different types of account access: single-tenant, multi-tenant, personal accounts or a combination of the latter two. Single tenant applications only allow users from the same tenant to issue an OAuth token to the app. Multi-tenant applications, on the other hand, allow any Azure tenant to issue an OAuth token to them. Therefore, app developers need to examine the tokens in their code and decide which user is allowed to log in.
“In the case of Azure App Services and Azure Functions, we see a textbook example of shared responsibility confusion. These managed services allow users to add authentication capability with the click of a button, a seemingly seamless process for the application owner. However, the service only ensures the validity of the token. Application owners don't realize that they are responsible for validating the user's identity via OAuth claims and providing access accordingly."
Microsoft reacted quickly and fixed the gap
“We found several highly effective, vulnerable Microsoft applications. One of these apps is a content management system (CMS) that powers Bing.com and allowed us not only to modify search results, but also to launch powerful XSS attacks on Bing users. These attacks could compromise users' personal information, including Outlook emails and SharePoint documents."
All issues have been reported to the MSRC team. Fixed the vulnerable applications, updated the customer guide and patched some AAD features to reduce customer exposure. The technical course of the attack is described in a blog.
More at WIZ.io
