Business email compromise (BEC) attacks are becoming more and more common. Hackers get into your mailbox via Dropbox.
Experts at Check Point Research warn about hackers using Dropbox documents to host credential harvesting websites. In the first two weeks of September, security experts observed 5.550 attacks of this type.
Email threats are becoming increasingly popular
In the first half of 2022, email attacks accounted for between 86 and 89 percent of all attacks in the wild. They are increasingly becoming hackers' preferred method of breaking into an environment, compared to web-based attacks.
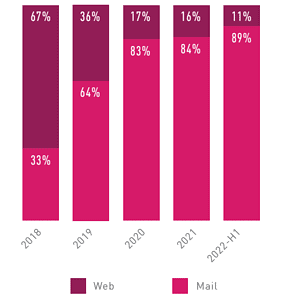
Comparison of the development of web-based and email attack routes in percent (Image: Check Point Research)
This increase in hacking activity has led to security solutions trying to find ways to improve their defenses. As security against various attacks improves, hackers must adapt.
One type of attack that has proven effective is brand impersonation, where a hacker makes an email appear to be from a trusted brand. Now hackers are ditching so-called “brand phishing” and trying real emails. The new way hackers are carrying out Business Email Compromise (BEC) 3.0 attacks is through legitimate services.
Tedious research or complex social engineering is no longer necessary. The hackers simply create a free account on a popular, reputable website and send links to malicious content directly from that service. These campaigns are currently storming email inboxes around the world.
Threat actors send links via Dropbox
The threat actors first share a file via Dropbox. To open the document, the end user must click “Add to Dropbox”. The link originally came from Dropbox, meaning there was nothing malicious in the initial communication. Dropbox is a legitimate website - there's nothing wrong with that. How the hackers use them is another story.
Once you click on Dropbox and log in, you can see the site hosted on Dropbox. Users must enter their email account and password to view the document. Even if users skip this step, the hackers have their email addresses and passwords.
Then, once users have entered their login details, they are redirected to a page that leads to a malicious URL. So the hackers have used a legitimate website to create two potential security holes: they obtain their victims' login details and then potentially trick them into accessing to click on a malicious URL. This is because the URL itself is legitimate. The content of the website is problematic. The hackers created a page that looks like it was created in OneDrive. When users click on the link, they download a malicious file.
Advice on protecting against BCE 3.0 attacks
What security professionals can do to protect their organization from these attacks:
- Implement security measures that check all URLs and emulate the underlying page.
- Educate users about this new variant of BEC attacks.
- Using AI-based anti-phishing software that can block phishing content across the productivity suite.
Most security services look at the sender, in this case Dropbox, see that it is legitimate and accept the message. That's because that's what the message appears to be.
In order to be prepared against this type of attack, various measures are required and a comprehensive security system is essential. Although this type of attack is launched via email, it then turns into a file sharing problem. Searching for malicious files in Dropbox and emulating links in documents is crucial. This includes replacing links in email body and attachments to ensure phishing attacks that use attachments with links are also prevented. This protection must apply every time a user clicks on the link.
Check Point Harmony Email researchers contacted Dropbox via the Report Phishing feature on May 15 to inform them of this attack and investigation.
More at CheckPoint.com
About check point Check Point Software Technologies GmbH (www.checkpoint.com/de) is a leading provider of cybersecurity solutions for public administrations and companies worldwide. The solutions protect customers from cyberattacks with an industry leading detection rate for malware, ransomware and other types of attacks. Check Point offers a multi-level security architecture that protects company information in cloud environments, networks and on mobile devices, as well as the most comprehensive and intuitive “one point of control” security management system. Check Point protects over 100.000 businesses of all sizes.
Matching articles on the topic
