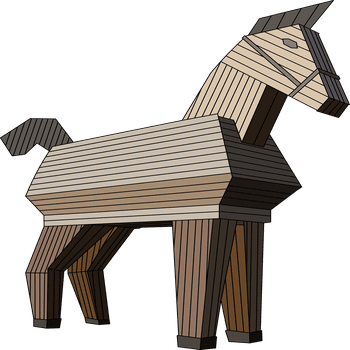
Security researchers discovered a fraudulent counterfeit of the popular software 3CX Desktop including malware or Trojan, a telephony system based on open standards. You can use it to make calls directly on the desktop with a headset.
The Trojan version now discovered contains a malicious DLL file that replaces an original file that comes bundled with the benign version of the application. When the fake application is loaded, the signed 3CX DesktopApp executes the malicious DLL as part of its predefined execution procedure. In this way, the harmless, popular VoIP application became a full-fledged malware that connects to third-party servers and is able to execute second-stage malware, thus loading malware onto the computer independently. According to the findings of the experts, it has already been unknowingly downloaded many times.
Multifunctional tool
3CXDesktopApp is a desktop client for 3CX's Voice over IP (VoIP) system. The application allows users to communicate inside and outside the company via their desktop or laptop. The program can record calls, enable video conferences and can be used on Windows, macOS and Linux operating systems, as well as cloud platforms. It's a tool companies use when they have a hybrid or distributed workforce. Customers include government service providers such as the UK Department of Health, as well as large corporations including Coca-Cola, Ikea and Honda. This is a classic supply chain attack, although at the time of writing there is no evidence of any compromise in the 3CXDesktopApp source code. Nobody expected that the application would be equipped with a malicious implant.
Attack on the supply chain
Lotem Finkelstein, Director of Threat Intelligence & Research at Check Point, on the current threat: “This is a classic supply chain attack designed to exploit relationships of trust between an organization and external parties, including partnerships with vendors or the use of software from third parties that most businesses rely on in some way. This incident reminds us of the importance of scrutinizing our business partners. Just asking what they're doing for your organization's cybersecurity can limit your organization's risk as threat actors compromise an organization and then work their way up the supply chain.
Custom Malware
Threat actors are constantly evolving their attack techniques, increasingly relying less on the use of custom malware and instead relying on non-signature-based tools. They leverage built-in operating system features already installed on the target's machine and leverage common IT management tools that raise less suspicion if detected. Commercial pentesting and red team tools are also often used. While this is not a new phenomenon, what used to be rare and reserved only for sophisticated actors is now a widespread technique employed by all threat actors. Looking ahead, it is important that we prioritize a consolidated, comprehensive and collaborative approach to security that protects our networks from the ever-changing cyber landscape.”
Check Point users can breathe easy: All software vulnerabilities and attack signatures found or sighted by Check Point Research, like this Trojan version of the original 3CX desktop app, are immediately routed to ThreatCloud, the brains behind all Check Point products, which spreads the appropriate protective measures across all Check-Point products. This means that all Check Point customers are immediately protected without patching. This is what happened in this case: as soon as the Trojan version of the 3CXDesktopApp client was reported, all relevant protections were integrated on all Check Point products.
More at Checkpoint.com
About check point Check Point Software Technologies GmbH (www.checkpoint.com/de) is a leading provider of cybersecurity solutions for public administrations and companies worldwide. The solutions protect customers from cyberattacks with an industry leading detection rate for malware, ransomware and other types of attacks. Check Point offers a multi-level security architecture that protects company information in cloud environments, networks and on mobile devices, as well as the most comprehensive and intuitive “one point of control” security management system. Check Point protects over 100.000 businesses of all sizes.
Matching articles on the topic
