
US is offering "up to $10 million" in rewards for information on the Conti gang and for capturing the "Fab Five" behind Conti. Behind the name Conti is a well-known ransomware gang - more precisely a so-called ransomware-as-a-service (RaaS) gang.
In the RaaS criminal business model, the part of ransomware code creation, extortion, and taking extortion payments from desperate victims is handled by a core group, while the attacks themselves are carried out by a loosely assembled “team” of members. And these are typically recruited not for their malware-programming skills, but for their phishing, social engineering, and network intrusion skills.
These "partners" pocket about 70 percent of the money extorted from victims. This is a significant incentive to attack and infect entire networks at once.
Targeted recruitment of gangs is commonplace
For example, about two years ago, the REvil ransomware gang offered a $1.000.000 advance on an underground hacker recruitment forum to recruit new affiliates for their cybercriminal activities. The corresponding REvil "Job Ad" sounded like a core team from RaaS. They were looking for “teams that already have experience and skills in penetration testing, msf/cs/koadic, nas/tape, hyper-v, and similar types of software and devices.”
The REvil gang had a particular interest in technologies such as NAS (Networked Attached Storage), or Hyper-V (Microsoft's virtualization platform), as with the appropriate expertise, for example, existing backups can be encrypted with everything else during an attack. This makes it harder than ever for victims to save themselves.
Mutiny on the Conti
However, the symbiotic relationships between the core members of a RaaS gang and the affiliated members they rely on are fragile. For example, just over a year ago, the Conti crew was struggling with a kind of mutiny within its own ranks, as one angry post revealed: "Yeah, of course they recruit suckers and split the money among themselves, and the boys will come along." fed what they will tell you when the victim pays," it said. One of the disgruntled partners had also released a large archive file related to the Conti gang entitled Мануали для работяг и софт.rar (manuals and software).
As for the background of the post, Sophos was able to find out at the time that at least some partners in the Conti ransomware scene did not receive 70% of the ransom money actually collected, but 70% of an imaginary but lower sum that was communicated to them by the core members of the Conti gang became.
US is offering a reward of up to 10 million
The United States has just officially and publicly offered a reward of "up to $10 million" under the catchphrase Conti. Excerpts from the justification: “First discovered in 2019, Conti ransomware was used in more than 1.000 ransomware operations targeting critical infrastructure in the US and worldwide, such as: B. law enforcement agencies, emergency medical services, emergency response centers and communities. Healthcare and first responder networks are among the more than 400 organizations worldwide that have been victims of Conti, more than 290 of them in the United States.”
The whistleblower reward is paid as part of a global US initiative to fight crime and terrorism known as Rewards for Justice (RfJ), administered by the US Diplomatic Service on behalf of the US Department of State. While it's unlikely that a single whistleblower in the Conti saga will claim the full $10 million, there are plenty of financial incentives for other whistleblowers to provide pertinent leads.
Who are the Fab Five?
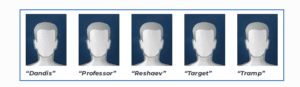
There do not seem to be any mug shots of the FabFive for visual identification. The Rewards for Justice page only shows dummies (Image: Sophos).
The RfJ program itself has been in existence for almost 40 years, and in that time it says it has paid out about $250 million to more than 125 different people worldwide, averaging about $2.000.000 in payouts about three times a year. Excerpt from a general description:
"The RfJ program offers a reward of up to $10 million for informationleading to the identification or location of an individual engaged in malicious cyber-activities against U.S. critical infrastructure in violation of the Computer Fraud and Abuse Act (CFAA), at the direction or under the control of a foreign government.” This time, the US However, the State Department has expressed an interest in five individuals currently known only by their underground names: Dandis, Professor, Reshaev, Target and Tramp. There don't seem to be any mug shots for visual identification.
More at Sophos.com
About Sophos More than 100 million users in 150 countries trust Sophos. We offer the best protection against complex IT threats and data loss. Our comprehensive security solutions are easy to deploy, use and manage. They offer the lowest total cost of ownership in the industry. Sophos offers award-winning encryption solutions, security solutions for endpoints, networks, mobile devices, email and the web. In addition, there is support from SophosLabs, our worldwide network of our own analysis centers. The Sophos headquarters are in Boston, USA and Oxford, UK.
