Trend Micro releases its security situation report mid-year. The increase in ransomware attacks on Linux and embedded systems is particularly striking: a 75 percent increase. The 2022 Midyear Roundup Report is freely accessible.
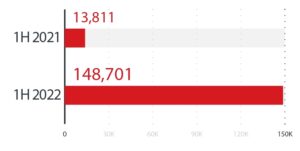
According to this, the company blocked a total of 2022 billion cyber threats in the first half of 63. All values at the increases in the first half of 2022 compared to the first half of 2021. The 75 percent increase in ransomware attacks on Linux systems is striking Based on these findings, the security experts expect that attacks on these systems will continue to increase in the coming years.
In the first half of 2022, the Japanese IT security specialist blocked 63 billion threats worldwide. This is an increase of 52 percent compared to the same period last year. The public sector, manufacturing, and healthcare were the top targets for malware attacks.
Ransomware remains the biggest threat
Detections of ransomware-as-a-service attacks skyrocketed in the first half of 2022, particularly from big players: LockBit saw a 500 percent year-on-year increase, while Conti's detections almost doubled in six months. In particular, the Ransomware-as-a-Service (RaaS) business model brought significant profits to ransomware developers and their partners (“affiliates”).
New ransomware groups are popping up all the time. The most conspicuous group in the first half of the year is called Black Basta. Within a period of just two months, these cybercriminals attacked as many as 50 companies. As the Trend Micro report findings show, many attacks continue to target large enterprises (“big-game hunting”), although small and medium-sized businesses (SMBs) are also becoming an increasingly popular target.
exploitation of vulnerabilities
One of the main attack vectors for ransomware is exploitation of vulnerabilities. Trend Micro's Zero Day Initiative (ZDI) published advisories for 944 vulnerabilities during the period, a 23 percent increase over the prior year. The number of published notices of critical bugs even increased by 400 percent year-on-year.
The results also show that Advanced Persistent Threat (APT) groups are evolving their methods by leveraging extensive infrastructure and combining different malware tools. The tenfold increase in the number of Emotet detections is further evidence that threat actors are increasingly incorporating this malware into their tactics.
There is concern that threat actors are increasingly able to exploit such vulnerabilities faster than vendors can release patch updates or companies can patch them. Unpatched vulnerabilities contribute to a growing digital attack surface that many organizations are grappling with. The rise in hybrid workplaces also continues to expand the IT environment. In fact, more than two-fifths (43 percent) of companies around the world believe it is “getting out of control,” according to a recent Trend Micro study.
Protection for a growing attack surface
Full visibility in the cloud is particularly important as cybercriminals exploit misconfigured environments, increasingly employing new techniques such as cloud-based cryptomining and cloud tunneling. In particular, cloud tunneling is often abused by attackers to route malware traffic or host phishing websites.
“New and emerging threat groups are evolving their business models and targeting their attacks with even greater precision. To reduce risk, organizations must better map, understand, and protect their growing digital attack surface,” said Jon Clay, vice president of threat intelligence at Trend Micro. "A unified cybersecurity platform is the best starting point for this."
More at TrendMicro.com
About Trend Micro As one of the world's leading providers of IT security, Trend Micro helps create a secure world for digital data exchange. With over 30 years of security expertise, global threat research, and constant innovation, Trend Micro offers protection for businesses, government agencies, and consumers. Thanks to our XGen™ security strategy, our solutions benefit from a cross-generational combination of defense techniques optimized for leading-edge environments. Networked threat information enables better and faster protection. Optimized for cloud workloads, endpoints, email, the IIoT and networks, our connected solutions provide centralized visibility across the entire enterprise for faster threat detection and response.