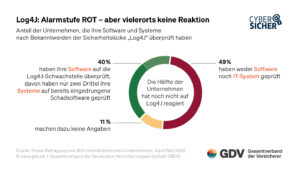
The majority of medium-sized companies have not yet got to the bottom of the Log4j or Log4Shell problem. Only 40 percent have addressed the problem. Tenable warns that medium-sized companies still have an immensely large attack surface.
As reported by the General Association of the German Insurance Industry (GDV), only 40 percent of medium-sized companies have so far checked their software to see whether it is affected by the Log4j vulnerability. Even fewer companies (28 percent) stated that they had checked their systems for intruded malware as a result of the vulnerability becoming known in December 2021.
“When Log4Shell (CVE-2021-44228) was first identified over six months ago, it rocked the IT security community. The fact that more than half a year later, more than half of German medium-sized companies are still in the dark as to whether their software is affected and therefore a security risk is worrying.
The warning went unheeded in large parts of the middle class
"Companies must not simply ignore such a vulnerability and the loud and clear warnings about it," says GDV General Manager Jörg Asmussen. After the security gap became known in December 2021, the Federal Office for Information Security (BSI) declared the highest alert level and spoke of an "extremely critical threat situation". "Anyone who doesn't react to this is too careless when it comes to IT security - or has too little know-how," says Asmussen. In case of doubt, companies could also lose their cyber insurance cover if hackers attack via an IT security gap that has been known for a long time but has not yet been closed.
High effort for more security
The problem is that while it's really difficult to sift through all the applications and services that use the vulnerable library, it's also easy for criminals to exploit them if they do. In December, when the vulnerability was first identified, Tenable's telemetry found that 10% of all assets assessed were vulnerable - that's not 10% of the organizations, but 10% of the applications and associated devices deployed there - including a variety of Servers, web applications, containers and IoT devices. At that time, every tenth element of our digital infrastructure had the potential for abuse by Log4Shell.
Given the ease of exploitation and the wide attack surface available, attackers will continue to use the vulnerability to gain a foothold to trigger targeted security breaches or automate opportunistic ransomware attacks, unless organizations finally take a proactive approach to Log4j.” said Roger Scheer, Regional Vice President for Central Europe at Tenable.
More at Tenable.com
About Tenable Tenable is a Cyber Exposure company. Over 24.000 companies worldwide trust Tenable to understand and reduce cyber risk. Nessus inventors have combined their vulnerability expertise in Tenable.io, delivering the industry's first platform that provides real-time visibility into and secures any asset on any computing platform. Tenable's customer base includes 53 percent of the Fortune 500, 29 percent of the Global 2000, and large government agencies.