According to Mandiant, a ransomware partner of ALPHV is increasingly looking for old vulnerabilities in Veritas backup installations. The gaps have actually been known since 2021 – but many of them have not been patched. It should currently be possible to find over 8.500 backup instances on the web.
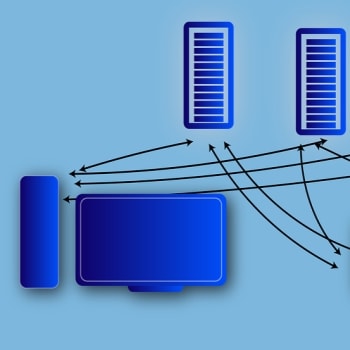
Mandiant has observed a new ALPHV ransomware partner (a.k.a. BlackCat ransomware) tracked as UNC4466 targeting public facing Veritas Backup Exec installations for vulnerabilities CVE-2021-27876, CVE-2021-27877 and CVE -2021-27878 are vulnerable. These CVEs have been known since March 2021 and patches are also available. However, some administrators have not yet implemented the patches.
8.500 Veritas Backup Exec instances in the network
A commercial Internet scanning service has identified over 8.500 installations of Veritas Backup Exec instances currently accessible via the Internet. It is possible that many of these systems are unpatched and therefore vulnerable. Previous ALPHV attacks investigated by Mandiant mainly relied on stolen credentials. This attack could be a shift in target by exploiting known vulnerabilities.
ALPHV emerged in November 2021 as ransomware-as-a-service, which some researchers claimed is the successor to BLACKMATTER and DARKSIDE ransomware. While some ransomware operators have issued rules to avoid impacting critical infrastructure and healthcare facilities, ALPHV has continued to target these sensitive industries.
Veritas vulnerability timeline
- In March 2021, Veritas released an advisory reporting three critical vulnerabilities in Veritas Backup Exec 16.x, 20.x, and 21.x.
- On September 23, 2022, a METASPLOIT module was released that exploits these vulnerabilities and creates a session through which the attacker can interact with the victim system.
- On October 22, 2022, Mandiant first observed exploitation of the Veritas vulnerabilities in the wild.
Administrators should definitely check their Veritas Backup Exec instances and close the gaps. Because it is becoming increasingly common for old, unpatched vulnerabilities to serve as a gateway for ransomware and the like. The last major attack on VMware ESXi servers was also exploited through an old vulnerability in non-modernized or patched versions.
In its blog, Mandiant shows how technically accurate the attack on the vulnerabilities in the Veritas Backup Exec installations is.
More at Mandiant.com
About Mandiant Mandiant is a recognized leader in dynamic cyber defense, threat intelligence and incident response. With decades of experience on the cyber frontline, Mandiant helps organizations confidently and proactively defend against cyber threats and respond to attacks. Mandiant is now part of Google Cloud.
