Three quarters of German companies were victims of cyber attacks with data loss at least once in the past year. The Trend Micro Cyber Risk Index shows that a lack of overview leads to an increased cyber risk for companies.
Trend Micro, one of the world's leading providers of cyber security solutions, publishes the results of its latest Cyber Risk Index (CRI) for the first half of 2022. In it, 76 percent of all companies surveyed in Germany state that they have experienced security incidents in the last twelve months as a result of which customer data has been lost or stolen.
29 percent more than 7 security incidents
In 29 percent there are even seven or more incidents. The proportion is just below the European value of 34 percent. Many companies found it particularly difficult to keep track of and defend against a constantly growing area of cyber attack.
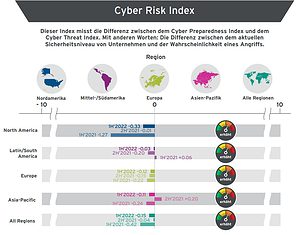
The biannual CRI (Cyber Risk Index) uses targeted questions to measure the discrepancy between the current security level of companies and the probability of an attack. From the information obtained, an index score is calculated on a numeric scale from -10 to 10, with -10 representing the highest level of risk. The global index rose from -0,04 in H2021 0,15 to -2022 in H2022 0,12, indicating rising cyber risk over the past six months. Broken down by region, the index shows a value of -XNUMX in Europe in the first half of XNUMX. This puts Europe just below the global cyber risk level, but also in the “increased” risk range.
More and more successful attacks worldwide
This trend is also reflected elsewhere in the data: The number of companies that were victims of a successful cyber attack worldwide rose from 84 percent to 90 percent in the same period. Not surprisingly, the number of organizations expecting to be hit by an attack in the coming year has also increased from 76 percent to 85 percent.
Some of the key risks highlighted in the report are related to an organization's attack detection capabilities. Security professionals often struggle to determine the physical location of business-critical data and applications.
Cybersecurity Goals vs. Business Goals
From a business perspective, the biggest concern is the lack of alignment between CISOs and senior management. The statement "My company's cybersecurity goals are aligned with the business goals" contained in the survey only achieved an approval rating of 4,31 out of 10 in Germany. A good quarter of the German respondents (27 percent) even completely contradicted this statement. Accordingly, a third of the German IT managers surveyed are convinced that the C-Level of their company does not see IT security as a priority.
“The CRI continues to provide an insightful snapshot of how global organizations assess their security posture and likelihood of attack. Given the current strong macroeconomic headwinds, the risk could not be greater,” explains Dr. Larry Ponemon, Chairman and Founder of the Ponemon Institute, which collects CRI on behalf of Trend Micro. "Participants cited the high cost of external expertise, disruption to critical infrastructure, and lost productivity as the top negative consequences of a security incident."
Poll: These cyber threats matter
- Fileless attacks
- Business Email Compromise (BEC)
- Botnets
- Cross-Site Scripting
- Denial of Service (DoS)
“You can't protect what you don't have an overview of. As hybrid working heralds a new era of complex, distributed IT environments, many organizations are struggling to close the growing gaps in their security landscape,” said Richard Werner, Business Consultant at Trend Micro. "To prevent the attack surface from spiraling out of control, they should combine the collection and monitoring of their systems with detection and response on a unified platform."
More at TrendMicro.com
About Trend Micro As one of the world's leading providers of IT security, Trend Micro helps create a secure world for digital data exchange. With over 30 years of security expertise, global threat research, and constant innovation, Trend Micro offers protection for businesses, government agencies, and consumers. Thanks to our XGen™ security strategy, our solutions benefit from a cross-generational combination of defense techniques optimized for leading-edge environments. Networked threat information enables better and faster protection. Optimized for cloud workloads, endpoints, email, the IIoT and networks, our connected solutions provide centralized visibility across the entire enterprise for faster threat detection and response.